
Windows blocks saving to specific folders—mainly system directories like Program Files and the Windows folder—to protect critical operating system files and maintain stability. This restriction operates through file permissions: system folders typically grant "read" but not "modify" or "write" access to standard user accounts. Only trusted processes (like installers run by administrators) gain elevated permission to alter these areas, preventing accidental deletions by users or unauthorized modifications by malware.
For example, software installers require administrative approval to write files into "Program Files," ensuring only verified applications modify this shared location. Similarly, applications cannot directly save user-specific settings or data in system folders; instead, they write to user-specific locations like "AppData" within the user's profile directory. This is crucial in corporate IT environments where user profiles roam across devices without affecting shared program files.
The primary advantage is enhanced security and system integrity, reducing the risk of corruption or exploits. However, a limitation is potential confusion for users or developers expecting applications to save freely everywhere. Legitimate software needing restricted access must be "run as administrator" or use virtualized write paths provided by UAC (User Account Control), balancing safety with functionality. Future developments may refine these permissions further for containerized or security-hardened environments.
Why does Windows block saving to certain folders?
Windows blocks saving to specific folders—mainly system directories like Program Files and the Windows folder—to protect critical operating system files and maintain stability. This restriction operates through file permissions: system folders typically grant "read" but not "modify" or "write" access to standard user accounts. Only trusted processes (like installers run by administrators) gain elevated permission to alter these areas, preventing accidental deletions by users or unauthorized modifications by malware.
For example, software installers require administrative approval to write files into "Program Files," ensuring only verified applications modify this shared location. Similarly, applications cannot directly save user-specific settings or data in system folders; instead, they write to user-specific locations like "AppData" within the user's profile directory. This is crucial in corporate IT environments where user profiles roam across devices without affecting shared program files.
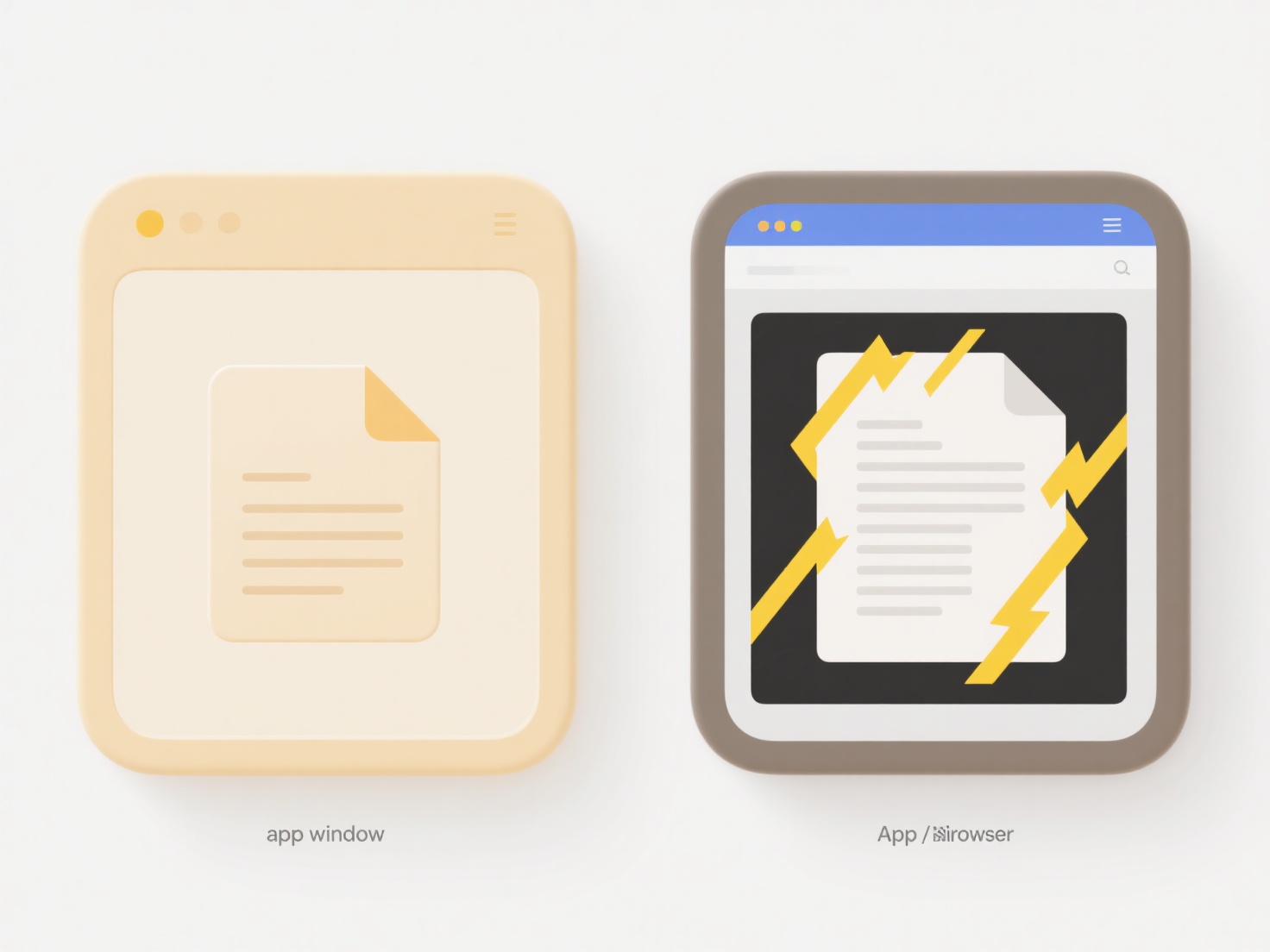
The primary advantage is enhanced security and system integrity, reducing the risk of corruption or exploits. However, a limitation is potential confusion for users or developers expecting applications to save freely everywhere. Legitimate software needing restricted access must be "run as administrator" or use virtualized write paths provided by UAC (User Account Control), balancing safety with functionality. Future developments may refine these permissions further for containerized or security-hardened environments.
Quick Article Links
How do I export a shared document to send by email?
Exporting a shared document refers to creating a standalone copy of that file in a standard format, separate from the or...
How do I rename files while keeping embedded metadata intact?
Renaming files typically refers to changing their displayed name without altering the file's core data content. Embedded...
How do I find large files taking up storage?
Finding large files involves identifying files that consume significant storage capacity on your computer or device. Unl...